If you see something, say something.
As of October 10, the U.S. Homeland Security Department had issued an alert about “multiple vulnerabilities” in a supervisory control and data acquisition (SCADA) monitoring system for solar energy platforms.
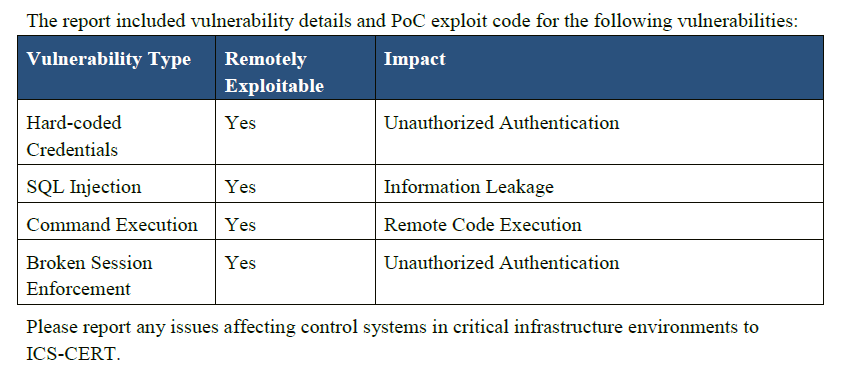
The department warns that unauthorized users may be able to access to the system and execute malicious code.
Two security consultants, Roberto Paleari and Ivan Speziale – both of whom have worked for the Milan-based computer and network security company, Emaze – discovered and reported the problems related to the Sinapsi Esolar Light Photovoltaic System Monitor, after contacting the vendor with no response.
Paleari and Speziale found that the Sinapsi eSolar Light Photovoltaic System Monitor installs remotely with a default password. The program authenticates users who provide the password of 36e44c9b64 (as well as one or two other unspecified passwords) – regardless of the username provided.
According to the consultants, “This allows attackers to trivially access the program or system and gain privileged access. Users are not able to change this password.”
The equipment also is sold under other product names, including Enerpoint eSolar Light, Schneider Electric (News - Alert) Ezylog Photovoltaic Management Server, Gavazzi Eos-Box and Astrid Green Power Guardian – all of which may share the same vulnerabilities.
Although a proof-of-concept (PoC) has been published by the pair of security pros, there have been no exploits to date. However, Paleari and Speziale wrote, “We are not aware of an updated firmware that corrects the issues described in this advisory. Users should avoid exposing the management interface of the device on the Internet.”
As the smart grid expands worldwide, security has become a major issue. Utilities and government agencies alike are aware that the electric infrastructure is more vulnerable today than ever before – and that extra security measures must be taken to protect it from hackers and terrorist organizations. Both the public and private sectors are working on the problem.
The alert was issued by the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) at Homeland Security.
 Internet Telephony Magazine
Click here to read latest issue
Internet Telephony Magazine
Click here to read latest issue CUSTOMER
CUSTOMER  Cloud Computing Magazine
Click here to read latest issue
Cloud Computing Magazine
Click here to read latest issue IoT EVOLUTION MAGAZINE
IoT EVOLUTION MAGAZINE




