It is no secret that the game has changed for enterprise security professionals as they strive to secure the rapidly evolving “mobile enterprise.” IT needs to authenticate/identify people, the devices they use, the applications on those devices, the networks they attach to, the data bases and business processes they interact with, and insure the integrity of data when it is at rest or on the move from end-to-end. In short, IT security people, literally and figuratively have their hands full.
In addition, as the inexorable trends of BYOD, virtualization, the cloud and mobility change the way we all interact personally and professionally, and because authentication is now the new perimeter for risk mitigation, as the vectors of vulnerability have exploded it has laid bare the realities that the old ways of securing the enterprise are insufficient.
The above is just the high-level list of pain points that IT professionals must address. The challenge is not only must they find practical and cost-effective technical solutions to those issues, but they must implement them in a manner that is not disruptive to end users who have high expectations and a low tolerance for being told NO! This has become a particular challenge given all of the above considerations as well as the speed at which the enterprise security landscape is changing, particularly in regards to mobility.
If you will pardon the intended pun, mobile security solution provider Mocana (News - Alert) has stepped into the breach with the launch of its Atlas™ extended enterprise platform. As , John Aisien, SVP Marketing and Corporate Development, told me, “If you are trying to rollout enterprise business applications we understood that we needed to provide an enterprise app experience that is same or better or than consumer. Without Atlas it is an unsolved problem.”
He continued, “Atlas makes it possible to secure an app with no impact on app developer or the end user. We have made it simple and secure with our app-centric approach and enhancing security end-to-end through the new appliance. The good news is that apps not burdened with authentication requirements which are multi-factored and we simultaneously increase security thanks to encryption and our app-wrapping technology (Mobile App Protection) wrapping. Plus we do so without forcing a fork lift of existing security functionality. It is a win/win/win for developers, IT and end users.”
The goal here, as Aisien noted, is to reshape traditional enterprise mobile security architectures and associated economics by delivering a simple and scalable security platform that will catalyze the mass adoption of enterprise mobile apps.
A comprehensive approach
The chart below illustrates the complexity that the Atlas platform in conjunction with the rest of the Mocana portfolio addresses.
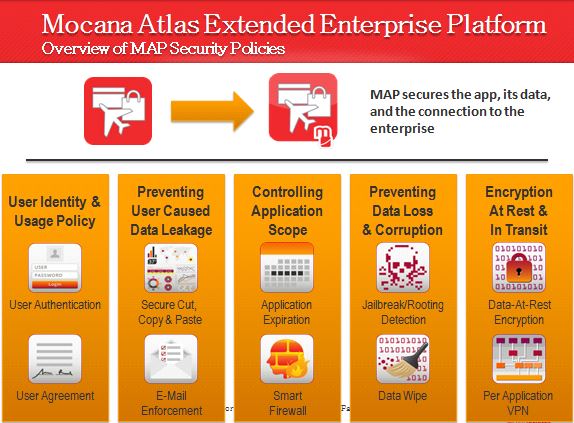
Source (News - Alert): Mocana (click to enlarge)
“With Mocana Atlas, we are remaking currently accepted enterprise mobility practices and moving beyond the poorly designed incumbent remote access solutions that belong to the era of laptops and PCs. Atlas is the first end-to-end platform that is purpose built to bring a true mobile app experience to organizations, at a fraction of today’s cost,” said Alan Panezic, vice president of products at Mocana. “We call this the Mocana ON (News - Alert) experience, where end users can connect to organizations’ secure perimeters from enterprise mobile apps as quickly and effortlessly as their usage experience with personal mobile apps. As a result, the Atlas platform empowers organizations to confidently embrace the exposure of their business and compliance-critical data to mobile applications from the edge of their networks.”
As can be seen in the above, the Atlas platform delivers the endpoint security, secure connectivity, termination and contextual policy enforcement capabilities that Mocana believes are just the ticket for driving enterprise mobile application adoption now and can scale to meet future needs.
The platform integrates the Mocana Atlas Appliance™, Mocana AtlasConnect, Mocana Mobile App Protection (MAP™) and Mocana Compass (News - Alert). Together, they provide:
- A complete, end-to-end solution for securing mobile applications and establishing secure, per-app connectivity with enterprise and cloud network perimeters, while empowering IT’s control mandate and end users’ needs for a native mobile application user experience.
- A simple solution at the edge that delivers fine-grained access control and easy integration with existing enterprise systems of enforcement and value.
- The scalability and performance needed to meet the demand for mobility by the extended enterprise, and the per-app connectivity architecture to satisfy the demand for enterprise mobile apps.
- Persistent management of all users’ per-app connectivity state at the edge, delivering an “always on” experience for all applications and across all supported device platforms.
- Dramatically lower enterprise mobility TCO.
“As corporate data is pulled to an increasing number of mobile devices, legacy laptop-era device and network-security tools fall short in BYOD deployments,” said Chris Hazelton, research director, enterprise mobility, at 451 Research (News - Alert). “Mobile application management with app-level VPNs allows IT to secure corporate data traffic. However, as an organization deploys a growing number of mobile apps, IT will need MAM offerings that can scale to support a large number of apps and users.”
How all of this fits together can be seen in the graphic below.
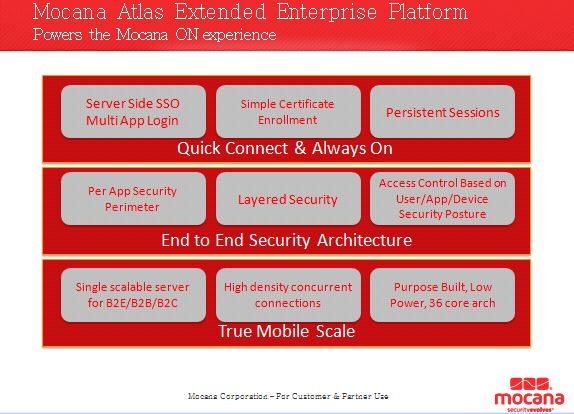
Source: Mocana (click to enlarge)
The Mocana Atlas extended enterprise platform is available and shipping now.
As Aisien noted, “Hard-binding of the user, the app and the device is critical. You need to create one integral domain of trust in which everything authenticated to everything else. What we have done is polled everything up to the app in order for that domain exist. We believe this is unique in the industry. The nice thing is customers will not have to rip and replace what they have. Plus, Atlas has pluggable interior security. We have created a virtualization layer at the edge and exposing at the device a uniform interface, one standard protocol for presenting itself for authenticity.”
And, in what is (pardon the pun) a wrap, Aisien noted that, “Usage patterns for mobile are different than at the desktop. Mobile can’t take any time used for authentication. Federating in the right way all authentication to support continuous use with the app as focal point of security where you login once and use forever is the logical way to ensure that domain of trust is always there to protecting the entire mobile enterprise environment.”
Edited by Maurice Nagle
Back to Mobile Secure
 Internet Telephony Magazine
Click here to read latest issue
Internet Telephony Magazine
Click here to read latest issue CUSTOMER
CUSTOMER  Cloud Computing Magazine
Click here to read latest issue
Cloud Computing Magazine
Click here to read latest issue IoT EVOLUTION MAGAZINE
IoT EVOLUTION MAGAZINE




